[Blog post updated on October 9, 2020 with reference to the new version 8.0 of the Microsoft 365 Security & Compliance – Single Slide]
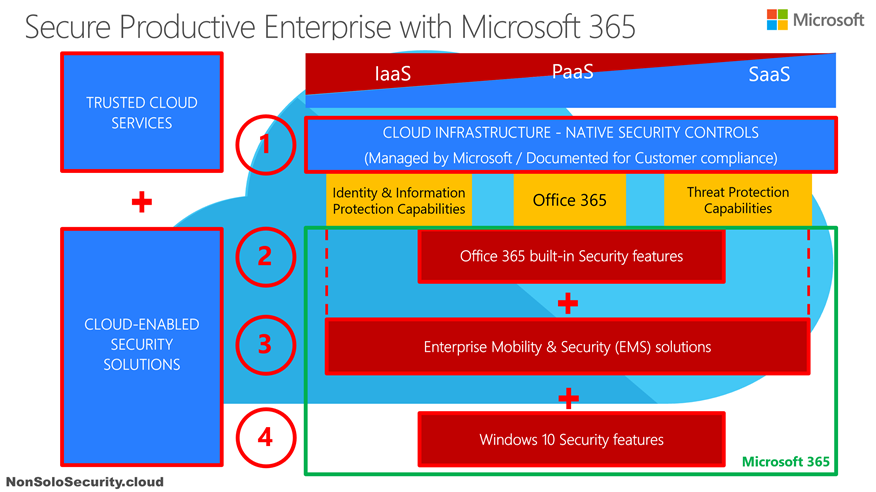
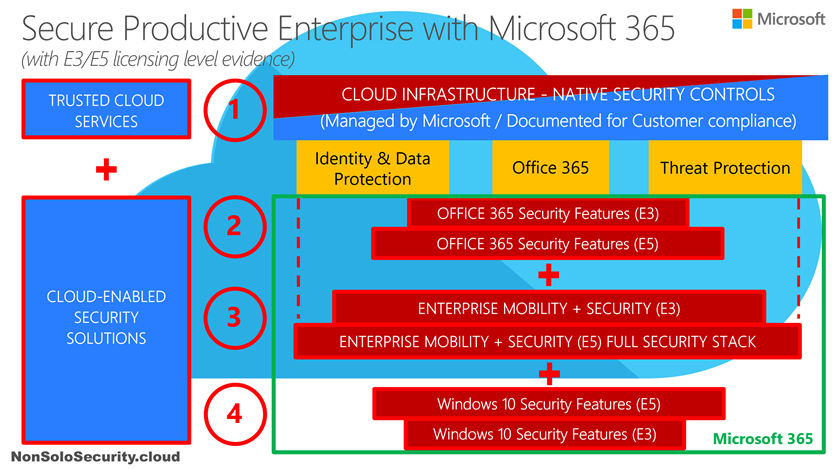
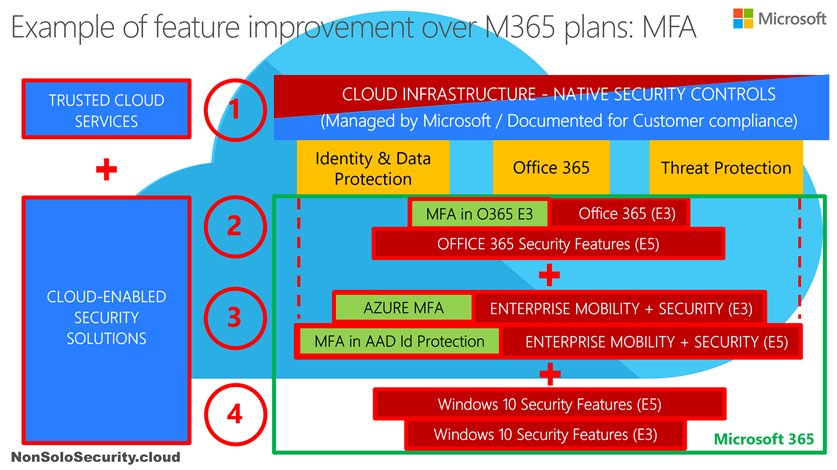
If you landed here, there’s the high probability that you’ve already read my previous blog post about the strategy behind the Microsoft 365 Security platform, (if this is not the case I strongly recommend to read it before going on) where I shared the layered approach of the Microsoft 365 security and compliance solutions to address the end-to-end stack from the device to the applications, with a very high level overview of suites and licensing levels inside Microsoft 365.
Now it’s time to reveal the full solution set with a more detailed level, the one that would be appreciated by a CISO who is wondering if Microsoft could be able to address most of her/his needs to secure the modern workplace.
First I have to share with you a couple of personal confidences: I’m quite obsessed by taxonomies (I like to give an order to the chaos in the universe :-), maybe because I’m an engineer?? ;-)) and inside Microsoft I’ve always fought for the principle of mastering end-to-end security (again testified by my 2nd post in the far January 2007) regardless any silos, job roles, business divisions, and company incentives.
Security must be applied and so learned end-to-end, in light of the defense in-depth principle, otherwise there isn’t any Security!
These explain why I started in the middle of 2016, well before the arrival of Microsoft 365 (see its announcement on July 2017), to build and share with colleagues and customers the idea of a Microsoft security platform, to highlight the value of several security features and solutions across Microsoft products and their increasing ability to integrate with each other to define a coordinated line of defense.
Additionally, I set the personal goal to use only a single PowerPoint slide to describe it, and this was the first prototype (ver. 0.1), dated in July 2016:

(If you are curious about later versions of this single slide you may find some examples in a previous blog post, when I celebrated 10 years of this blog).
Now you may understand my personal satisfaction when we later announced Microsoft 365 (see its announcement on July 2017): someway I was really looking forward our security strategy!
After almost 3 years of huge Microsoft investments in Security, with direct product development and several acquisitions (mainly looking for innovative Israeli cybersecurity companies…), the “single slide” personal goal I set in 2016 has become a daunting challenge!!
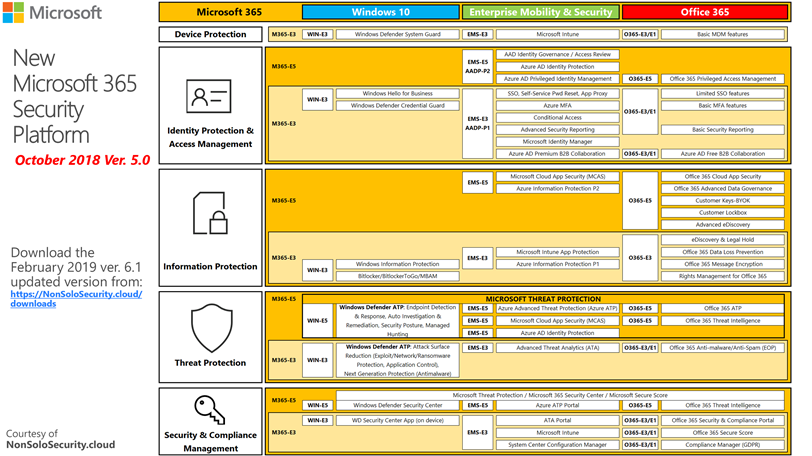
Here is a snapshot of one of the latest efforts, specifically the October 2018 version v.5.0 (which it is not the latest, see below for updates!) just built after the Ignite 2018 announcements:
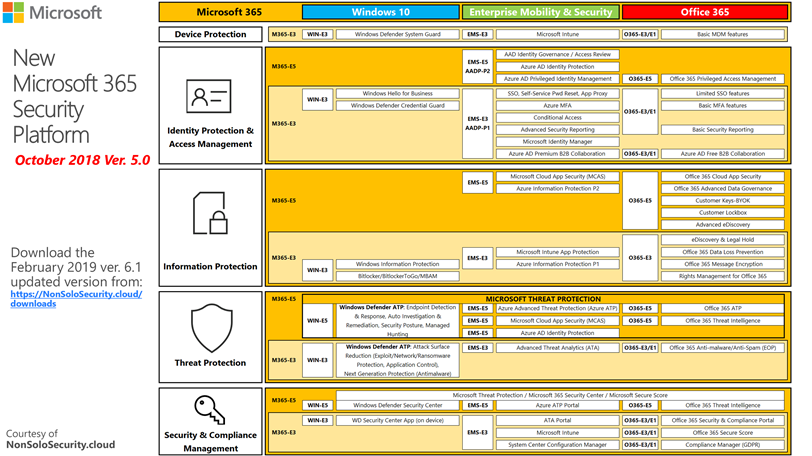
I have to say (with a bit of deep pride :-)) that out of dozens of PowerPoint slides I may use to pitch the value of our new Microsoft 365 Security platform, this is the single one slide that everyone wants to take-away as soon as possible, preferably right at the end of meeting!
Last month I updated it at the February 2019 version v.6.1 and you can now download it from the downloads page of this blog: this version has been enhanced with short description screentips and hyperlinks to the technical documentation by simply hovering and clicking with your mouse pointer over the single solution when viewing the slide in presentation mode.
March 21, 2019 update: slide version is now v.6.3 with latest announcements.
January 9, 2020 update: slide version is now v.7.0 with plenty of new additions & improvements. With this version I started to add detail slides (currently 9) to enlarge sections, improve font readability and simplify hyperlinking to technical documentation for every product / solution.
October 8, 2020 update: slide version is now v.8.0 with several updates, mainly about changes in the Microsoft 365 E5 Compliance bundle and announcements at Microsoft Ignite 2020.
I hope you can find it useful to map how Microsoft 365 can cover almost any end-to-end security and compliance needs to secure the Modern Workplace!
Of course you can expect I will build something similar for other Microsoft Security technologies , so stay tuned!
Ciao!
Feliciano